Secure Cloud Services Management is critical in today’s digital landscape. Organizations must implement stringent security protocols to protect sensitive data from unauthorized access. This involves leveraging encryption, access controls, and continuous monitoring. A tailored security strategy is essential for adapting to emerging threats. However, many organizations overlook the importance of employee training in fostering a culture of security awareness. Understanding these elements could be the key to achieving comprehensive protection.
Understanding the Basics of Secure Cloud Services Management
The foundation of secure cloud services management lies in a comprehensive understanding of both security protocols and cloud architecture.
Effective cloud compliance ensures that organizations adhere to regulatory standards, while robust data encryption safeguards sensitive information.
Essential Best Practices for Cloud Security
Effective cloud security management requires adherence to established best practices that enhance the overall security posture of organizations using cloud services.
Implementing data encryption safeguards sensitive information, while robust access control mechanisms ensure that only authorized users can access critical resources.
These practices not only mitigate risks but also empower organizations to maintain control over their data in an increasingly dynamic cloud environment.
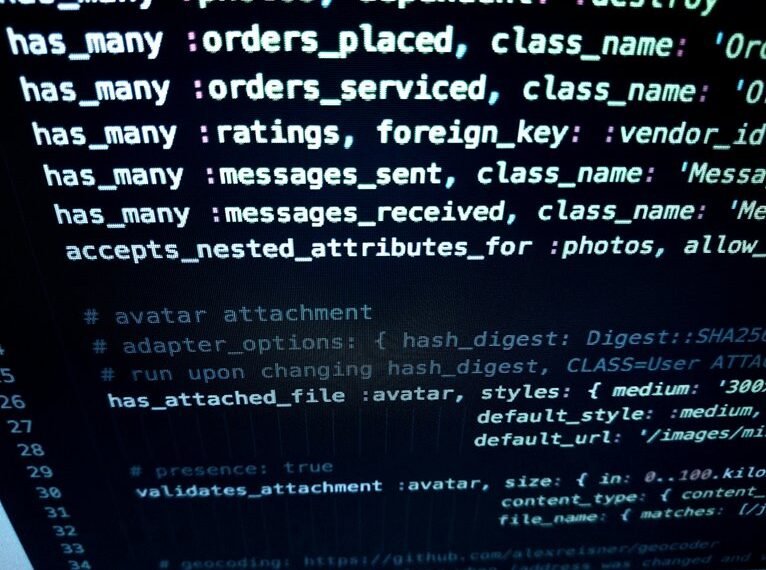
Tools and Technologies to Enhance Cloud Security
While many organizations recognize the importance of cloud security, leveraging the right tools and technologies is crucial for establishing a robust defense against potential threats.
Effective cloud security can be enhanced through advanced encryption techniques that safeguard data integrity and confidentiality.
Additionally, comprehensive access controls ensure that only authorized personnel can access sensitive information, significantly mitigating risks associated with unauthorized access and data breaches.
Developing a Robust Cloud Security Strategy for Your Organization
A robust cloud security strategy is fundamental for organizations aiming to protect their data in an increasingly digital landscape.
This involves a thorough risk assessment to identify vulnerabilities and potential threats. Additionally, aligning with established compliance frameworks ensures adherence to regulatory requirements.
Conclusion
In an era where data breaches loom ominously, the imperative for secure cloud services management cannot be overstated. As organizations navigate the complexities of cloud security, the stakes continue to rise. Will they adopt comprehensive strategies and cutting-edge tools in time to thwart potential threats? The future of sensitive information hangs in the balance, reliant on proactive measures, employee vigilance, and an unwavering commitment to security. Without decisive action, the consequences could be dire, leaving organizations vulnerable in a perilous digital landscape.